A woman in an online fetish community says she identified Kristi Noem’s husband with a pocket dial and a Google search. The public never saw the vetting system do the same.
One of the women allegedly pocket-dialed him. She heard a voicemail: “Noem Insurance, leave a message.” She Googled the business. She found Kristi Noem.
That is how a woman in an online fetish community says she discovered that the man she had allegedly been communicating with under the name “Jason Jackson” was the husband of the former Secretary of Homeland Security. Not through an intelligence briefing. Not through a classified leak. Through a pocket dial and a search engine.
The woman told the Daily Mail she was stunned. “I was completely shocked,” she said. “I thought, you should care — your wife could lose everything she’s ever worked for.”
What the Daily Mail Found
The Daily Mail’s investigation, published after Noem’s DHS tenure ended, alleged that her husband Bryon had been active in an online fetish community for at least 14 months — effectively the span of her time running one of the federal government’s biggest security and law-enforcement departments. He allegedly used a pseudonym, sent photos of himself, and paid the women at least $25,000 through PayPal and Cash App.
When the Daily Mail reached Bryon by phone, he did not reportedly deny the photos or the conversations. He denied that his behavior created a national-security risk. A representative for Kristi Noem told People the family was “blindsided” and “devastated.” Trump told Entertainment Weekly he felt “badly for the family.”
None of that is the real story. The real story is what this says about the system that was supposed to surface vulnerability before it became public spectacle.
The Clearance Process Exists for Exactly This


The federal personnel-security system is supposed to catch vulnerabilities, not just crime. The SF-86 collects spousal information. The government’s adjudicative guidelines explicitly treat sexual behavior and personal conduct as security concerns when they could expose someone to coercion, exploitation, or duress.
If the Daily Mail’s reporting is accurate, Bryon Noem was allegedly using a pseudonym to communicate with women online, sending money through traceable digital platforms, and sharing photos that could have created leverage over the person overseeing ICE, CBP, the Secret Service, TSA, FEMA, and CISA.
Former CIA officer Marc Polymeropoulos told the Daily Mail that if a media organization could find this information, a hostile intelligence service almost certainly could too. Megyn Kelly said on her show that if this had been known, Kristi Noem “never would have been confirmed for that post.” The Daily Mail also cited unnamed DHS officials saying the same thing.
That is not coming only from liberal critics. It is coming from a former CIA officer, a conservative commentator, and unnamed DHS officials cited by the outlet. The vetting system either missed the issue, did not appreciate it, or never surfaced it in public.
The Tip Came From Inside the System’s Own Target List
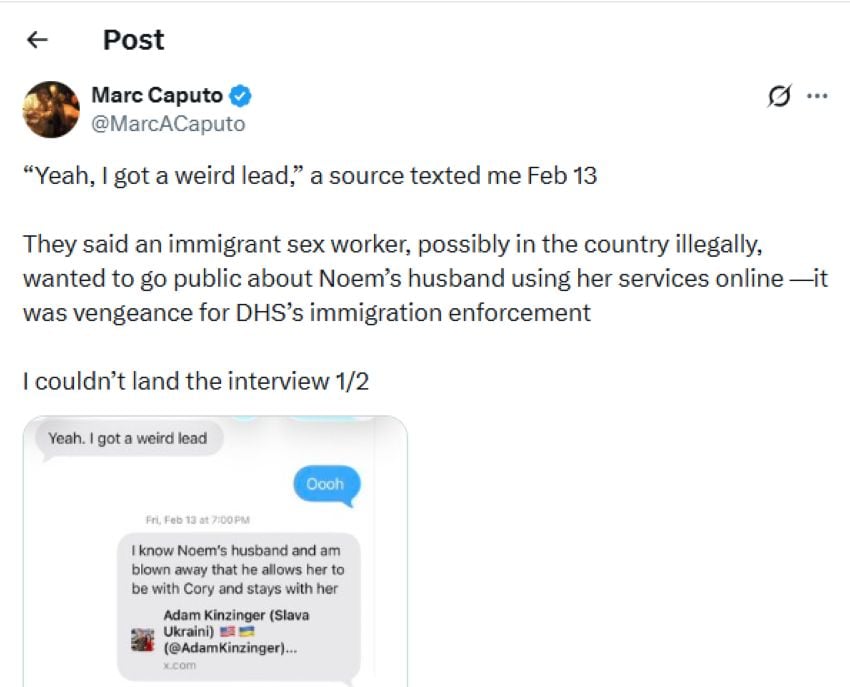
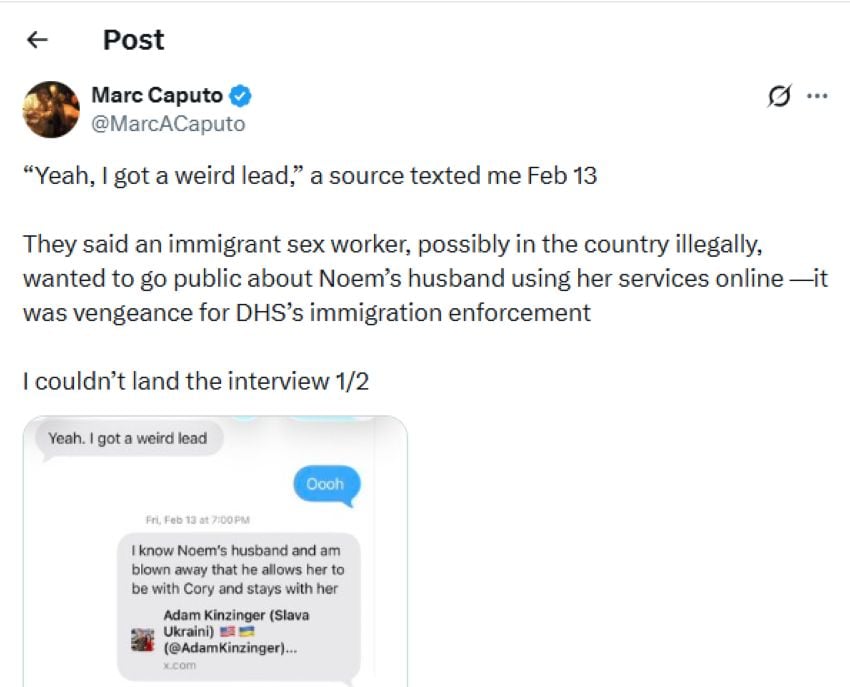
This is the detail that makes the story curdle. Daily Beast reporting on a post from Axios reporter Marc Caputo said he got a tip back in February about Bryon Noem’s online activity from what he described as an immigrant sex worker who was possibly in the country illegally. Caputo said the source wanted revenge for DHS immigration enforcement under Noem.
Read that again. The woman who oversaw ICE may have been carrying a family vulnerability that, according to Caputo’s account, first surfaced through someone in the very population her department was targeting. Caputo said he could not land the interview at the time. The Daily Mail could and did.
The Question Is Not the Fetish
What Bryon Noem does in his private life is, in isolation, between him and his family. That is not what this piece is about. This piece is about the possibility that the DHS secretary’s immediate family carried a documented, traceable, and potentially exploitable vulnerability for 14 months — one involving a pseudonym, digital payments, and a photographic trail — while she held one of the most sensitive jobs in the federal government.
The family says they were blindsided. Maybe they were. But the vetting process is not supposed to be blindsided by a possible coercion risk. That is one of its core jobs. If a woman in a fetish community says she discovered the connection through a pocket dial and a Google search, and a tabloid reporter advanced it with a phone call, then the question the government needs to answer is not what Bryon Noem was doing online. The question is whether anyone in the security-vetting chain bothered to look.
Because if the answer is no, then for 14 months the person running America’s homeland security apparatus may have been carrying an undetected vulnerability that a fetish-community contact found by accident, a journalist advanced in days, and a hostile intelligence service might have exploited at any time. That is not just a scandal about a marriage. It is a stress test for the system designed to prevent exactly this.